Secure your offchain infrastructure
Even the most secure smart contract can be undone by a single vulnerable offchain component. OpenZeppelin brings reliability and resilience to every line of your infrastructure code.
Trusted by leading institutions and DeFi innovators
The challenge
Why offchain code keeps you up at night
Endless, Complex Codebase
Offchain codebases are often complex and massive, making it difficult and expensive to ensure reliability and security.
Fixing in Production
While offchain components can be easily fixed after vulnerabilities are discovered, malicious actors can spot flaws before you do.
Frequent Code Updates
If you are releasing frequent updates or changes to infrastructure code, you need to be sure you haven’t introduced vulnerabilities.
Our Approach
OpenZeppelin’s tailored and targeted infrastructure security
Elite Expertise First
Every review is led by veteran researchers who live and breathe blockchain infrastructure.
We Know Where to Look
Drawing on our expertise, we identify and focus on specific components and modules where exploits are most likely to occur.
Risk-Weighted Scoping
Each component is graded for criticality and complexity, so time and budget go toward business-critical logic, not low-impact boilerplate.
Our Infrastructure Security Researchers have deep expertise in various languages and technologies.


The Solutions
Security
Assessments & Audits
We only do what is needed to make your infrastructure safe, ensuring clients' protocols remain secure without exceeding their budgets.
Security Assessment
Identify high-level flaws, architectural problems, and the most critical areas a subsequent audit should focus on. Ideal for projects in late-development stages or with very large codebases. Though an assessment is not an audit engagement, it can be critical to identify and strengthen key areas before moving on to an audit.
Security Audit
A deep, comprehensive code review to uncover security issues and provide recommendations for safe deployment. Usually performed in different phases on multiple subscopes, previously identified during the Security Assessment.
Uncovered
Performed
Locked secured
Next Steps
We'll review your code, assess your infrastructure's maturity and complexity, and develop a tailored plan that fits your needs, timeline, and budget.
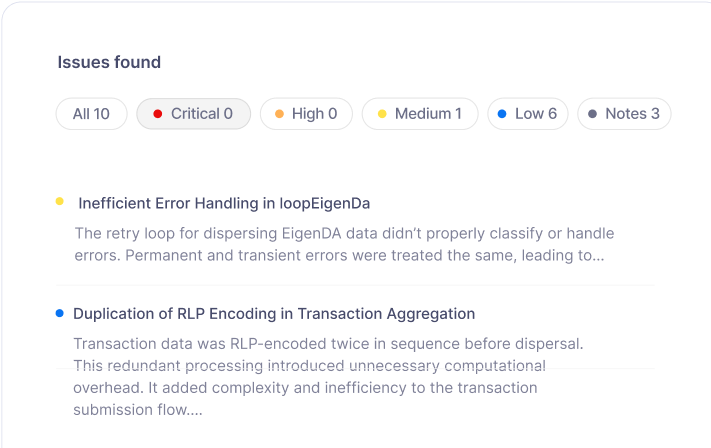
Infrastructure Audits in action
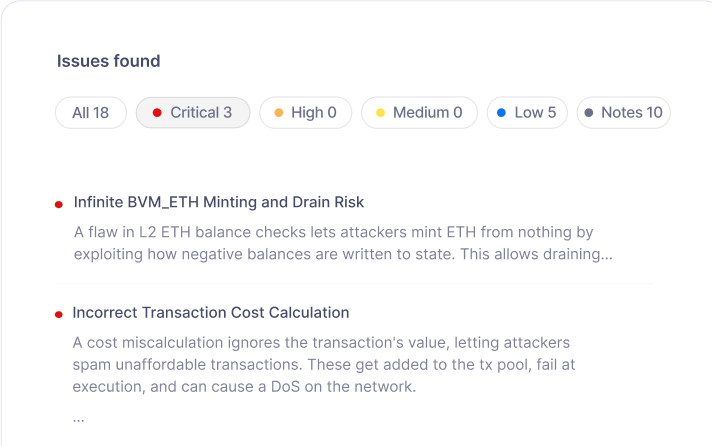
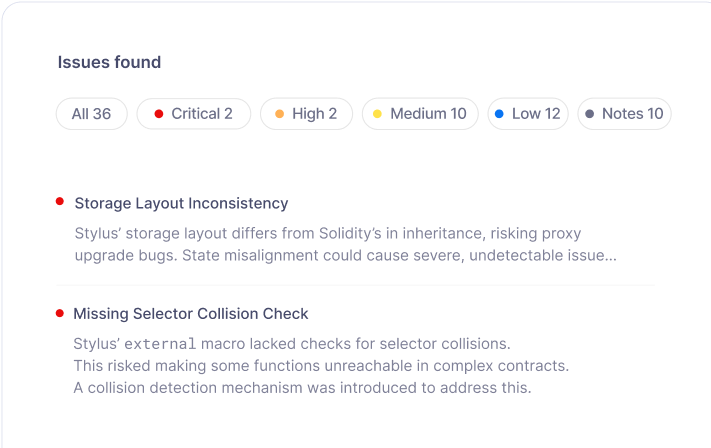
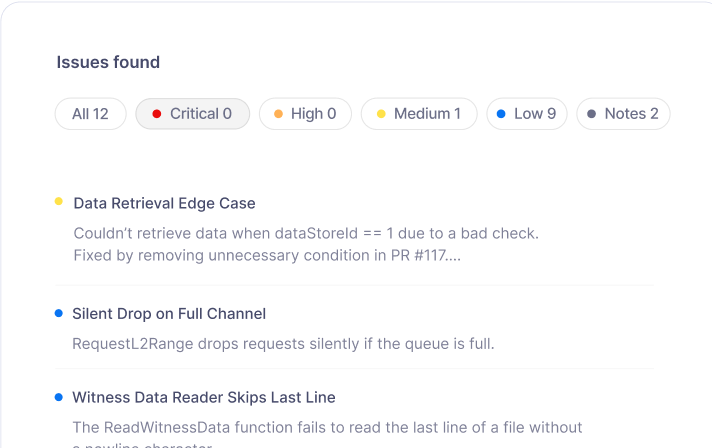
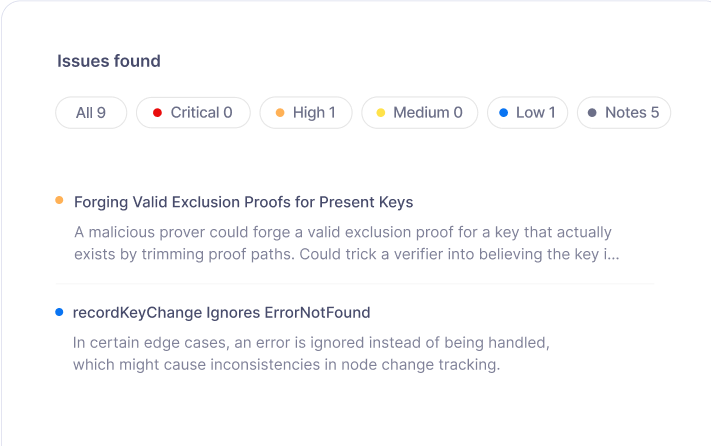
Dive into real public reports and see how our findings translated into safer offchain infrastructure for leading blockchain companies.